Saturday, February 23, 2013
(guardian)
A new global campaign to persuade nations to ban "killer robots" before they reach the production stage is to be launched in the UK by a group of academics, pressure groups and Nobel peace prize laureates.
Robot warfare and autonomous weapons, the next step from unmanned drones, are already being worked on by scientists and will be available within the decade, said Dr Noel Sharkey, a leading robotics and artificial intelligence expert and professor at Sheffield University. He believes that development of the weapons is taking place in an effectively unregulated environment, with little attention being paid to moral implications and international law.
The Stop the Killer Robots campaign will be launched in April at the House of Commons and includes many of the groups that successfully campaigned to have international action taken against cluster bombs and landmines. They hope to get a similar global treaty against autonomous weapons.
"These things are not science fiction; they are well into development," said Sharkey. "The research wing of the Pentagon in the US is working on the X47B [unmanned plane] which has supersonic twists and turns with a G-force that no human being could manage, a craft which would take autonomous armed combat anywhere in the planet.
"In America they are already training more drone pilots than real aircraft pilots, looking for young men who are very good at computer games. They are looking at swarms of robots, with perhaps one person watching what they do..."
(more)
Tuesday, February 19, 2013
(foreignpolicy)
Chinese government officials considered using an armed unmanned aerial vehicle to target a drug trafficker hiding in Myanmar, according to an interview with Liu Yuejin, the director of China's Public Security Ministry's anti-drug bureau that appeared in Global Times on Monday. The target, Naw Kham, wanted for a drug-trafficking related attack that killed 13 Chinese sailors, was eventually captured last April in a joint Chinese-Laotian operation in Laos and is now appealing a death sentence in China. Yuejin's comments are an unusual glimpse into China's considerations for the use of drone strikes, a tactic that is no longer used exclusively by the United States.
The proposed Chinese strike would have occurred in Myanmar's restive north, where the Naypyidaw government has struggled to control ethnic conflicts and a thriving drug trade. Much like the U.S. official rationale as for strikes in Pakistan, Yemen, and Somalia, China could have either sought Naypyidaw's support or credibly claimed that the government was "unwilling or unable to suppress the threat posed by the individual being targeted," in the words of the Obama administration's white paper on its own targeted killing program. Similarly, as a violent drug trafficker tied to the deaths of Chinese sailors, China could have justified the potential drone strike under the white paper's loose definition of the "imminent threat of violent attack" against the homeland -- much as the United States justified targeting al Qaeda militants tied to the bombing of the USS Cole with drone strikes, beginning Abu Ali al-Harithi in 2002 (well before the white paper was authored).
The admission that the Chinese government considered a drone strike comes as its relationship with Myanmar has become increasingly strained amid stalled economic projects and new competition for influence with the West. China also appears to have placed special emphasis on their UAV programs in recent months, unveiling new models (that look suspiciously like U.S.-made Predator and Reaper drones) and retrofitting old Shenyang J-6 jets to fly by remote control.
Yuejin told Global Times that the drone strike option was passed over because of instructions to capture Naw Kham alive, but his comments demonstrate that China is weighing targeted killings seriously. When -- almost certainly not "if" -- China conducts its first drone strike, it will join just three other nations -- the United States, Britain, and Israel -- and place itself among the drone powers in the ongoing international assessment of the legality of these operations and whether they abridge international law and the established concept of sovereignty...
(more)
(globalresearch)
In written responses to questions submitted by the Senate Intelligence Committee, John Brennan, the Obama administration’s nominee for director of the Central Intelligence Agency (CIA), refused to rule out drone assassinations of American citizens on US soil. The committee on Friday released a declassified version of Brennan’s responses.
Brennan, currently President Obama’s chief counterterrorism adviser, is the architect and director of the program of drone missile assassinations that is run out of the White House with the personal participation of Obama. Asked squarely, “Could the Administration carry out drone strikes inside the United States?” Brennan replied, “This Administration has not carried out drone strikes inside the United States and has no intention of doing so.”
This is what is known as a non-responsive answer. It is reasonable to assume that if the answer was “no,” Brennan would simply have written, “no.” Instead, in order to avoid a giving straightforward “yes,” he answered a different question than the one that was asked.
Brennan’s answers to the written questions make clear that there was nothing accidental about his refusal to rule out drone assassinations within the United States at his February 7 confirmation hearing before the Senate committee. It was, rather, an expression of a deliberate policy adopted by the Obama White House and the military/intelligence agencies.
When asked at the hearing whether he believed that the Obama administration could carry out drone assassinations on US soil, Brennan responded that he was determined to “optimize transparency on these issues, but at the same time, optimize secrecy and the protection of our national security.” He thus completely evaded the question, and no member of the committee, Democrat or Republican, pursued the matter further.
The very real threat of presidential assassinations of US citizens and others within the United States starkly raises the specter of police-military dictatorship. Behind the legalistic double-talk of the administration’s white paper on drone killings of Americans, made public two weeks ago, the US government is claiming unlimited powers to assassinate anyone, anywhere in the world...
(more)
(theatlantic)
An Air Force simulation says researchers are at work on killer robots so tiny that a group of them could blend into a cityscape.
Science writer John Horgan's feature on the many ways drones will be used in coming years is interesting throughout, and terrifying in the passage where he describes an effort to build micro-drones that are, as the U.S. Air Force describes them, "Unobtrusive, pervasive, and lethal."
Air Force officials declined a request to observe flight tests at a "micro-aviary" they've built, he reported, but they did let him see a video dramatization "starring micro-UAVs that resemble winged, multi-legged bugs. The drones swarm through alleys, crawl across windowsills, and perch on power lines. One of them sneaks up on a scowling man holding a gun and shoots him in the head."
When I watch that simulation I am horrified. I also think to myself, this technology is more likely to diminish American security than to enhance it. In a world without micro-drones, our military remains overwhelmingly powerful. But what about a world where micro-drones are pervasive? Who knows? Sure, we have a technological advantage right now, but micro-drones sure seem like a disruptive technology that will eventually help rather than hinder attempts at asymmetric warfare.
Yet the U.S. government is making no effort to enlist other powerful nations with the most to lose and establish international norms against the use of drones (in the way we've stigmatized biological weapons) -- rather, we're continuing to fuel a drone arms race that guarantees widespread proliferation. Perhaps such an effort would fail, but to never even try seems shortsighted...
(more)
(slate)
It was described recently by one rights group as a “secretive new surveillance tool.” But documents just released by the FBI suggest that a clandestine cellphone tracking device known as the “Stingray” has been deployed across the United States for almost two decades—despite questions over its legality.
Stingrays, as I’ve reported here before, are portable surveillance gadgets that can trick phones within a specific area into hopping onto a fake network. The feds call them “cell-site simulators” or “digital analyzers,” and they are sometimes also described as “IMSI catchers.” The FBI says it uses them to target criminals and help track the movements of suspects in real time, not to intercept communications. But because Stingrays by design collaterally gather data from innocent bystanders’ phones and can interrupt phone users’ service, critics say they may violate a federal communications law.
A fresh trove of FBI files on cell tracking, some marked “secret,” was published this week by the Electronic Privacy Information Center. They shed light on how, far from being a “new” tool used by the authorities to track down targets, Stingray-style technology has been in the hands of the feds since about 1995 (at least). During that time, local and state law enforcement agencies have also been able to borrow the spy equipment in “exceptional circumstances,” thanks to an order approved by former FBI Director Louis Freeh.
EPIC, a civil liberties group, obtained the documents through ongoing Freedom of Information Act litigation that it is pursuing in order to get the feds to hand over some 25,000 pages of documents that relate to Stingray tools, about 6,000 of which are classified. The FBI has been drip-releasing the documents monthly, and there have been a couple of interesting nuggets in the batches so far—like a disclosure that the FBI has a manual called “cell tracking for dummies” and details hinting that the feds are well aware the use of Stingrays is in shaky legal territory...
(more)
(guardian)
What impact will automation – the so-called "rise of the robots" – have on wages and employment over the coming decades? Nowadays, this question crops up whenever unemployment rises.
In the early nineteenth century, David Ricardo considered the possibility that machines would replace labour; Karl Marx followed him. Around the same time, the Luddites smashed the textile machinery that they saw as taking their jobs.
Then the fear of machines died away. New jobs – at higher wages, in easier conditions, and for more people – were soon created and readily found. But that does not mean that the initial fear was wrong. On the contrary, it must be right in the very long run: sooner or later, we will run out of jobs.
For some countries, this long-run prospect might be uncomfortably close. So, what are people to do if machines can do all (or most of) their work?
Recently, automation in manufacturing has expanded even to areas where labour has been relatively cheap. In 2011, Chinese companies spent 8bn yuan (£8.37bn) on industrial robots. Foxconn, which build iPads for Apple, hopes to have their first fully automated plant in operation sometime in the next five-to-10 years.
Now the substitution of capital for labour is moving beyond manufacturing. The most mundane example is one you will see in every supermarket: checkout staff replaced by a single employee monitoring a bank of self-service machines. (Though perhaps this is not automation proper – the supermarket has just shifted some of the work of shopping on to the customer.)
For those who dread the threat that automation poses to low-skilled labour, a ready answer is to train people for better jobs. But technological progress is now eating up the better jobs, too. A wide range of jobs that we now think of as skilled, secure, and irreducibly human may be the next casualties of technological change...
(more)
Saturday, February 16, 2013
(mashable)
The Pentagon wants soldiers to be able to scan people's faces, eyes and thumbs with their smartphones.
That's why the Department of Defense has inked a $3 million deal with California-based tech company AOptix, to develop its "Smart Mobile Identity System," as first reported by Wired's Military blog Danger Room.
AOptix is working on a tool that can be added to a regular smartphone and turn it into a device that can scan eyes, thumbs, voices, and faces. "They’ve asked us, based on what they’ve seen of our product, to work on some more specific needs and requirements for DoD," Chuck Yort, AOptix’s vice president for identity solutions, told Wired.
The Smart Mobile Identity System will be able to scan those biometrics at a certain distance, and do so much more easily than current systems like the Handheld Interagency Identity Detection System (HIIDE), that consists of a bulky camera. AOptix's device will be considerably smaller, since it's supposed to simply wrap around a smartphone.
The company now has two years to develop the hardware system as well as the software to complement it...
(more)
Thursday, February 14, 2013
(news.com.au)
Every time you purchase an app on Google Play, your name, address and email is passed on to the developer, it has been revealed.
The "flaw" - which appears to be by design - was discovered by Sydney app developer, Dan Nolan who told news.com.au that he was uncomfortable being the custodian of this information and that there was no reason for any developer to have this information at their finger tips.
You may remember Mr Nolan as the creator of the Paul Keating insult generator all that hit number one in the Aussie App Store last month."
"Let me make this crystal clear, every App purchase you make on Google Play gives the developer your name, suburb and email address with no indication that this information is actually being transferred," Nolan wrote on his blog.
"With the information I have available to me through the checkout portal I could track down and harass users who left negative reviews or refunded the app purchase."
Harrassment aside, the problems posed by malware - "virus" programs that infect your phone, or computer and steal your personal details - are far more serious.
With Google customers' details just sitting in developers accounts, all it would take is a half decent piece of malware software for that information to be accessed. These personal details could then be used to access the users' bank details. That's also more than enough information to be able to access your other devices which could also be mined for more data - insurance information, other credit cards - which could then be used to access your banking credentials.
Mr Nolan told News.com.au that tens of millions of Google customers could be affected.
"As far as I can tell this impacts every person who purchased an App on the Play Store," he said...
(more)
Monday, February 11, 2013
(gulfnews)
The UAE has built its national population register which is the world’s largest civil biometric database, a senior official said on Monday.
“The UAE population register system, the wold’s largest civil biometric database, was completed by the end of last year,” Dr Ali Al Khoury, director general of the Emirates Identity Authority, told the sixth ID World Abu Dhabi being held at the Emirates Centre for Strategic Studies and Research.
The two-day summit tackles the ICT challenges in modern society, bringing together high-level international government representatives and leading players in security, mobility and traceability.
Dr Al Khoury said on the sidelines of the World ID Summit that the UAE’s biometric database had a total of around 140 million fingerprints, palm and hand prints, facial prints and digital signatures which belonged to citizens and residents from more than 206 nationalities, but declined to disclose the population census figure or whether any other official assessment of the country’s population was accurate...
(more)
(cbs)
PHILADELPHIA – Is the Nutter Administration doing enough to expand its use of surveillance cameras to deter crime? That’s what City Council members will be looking at during a hearing later today. Administration officials are not taking part.
Today’s hearing was called by Council President Darrell Clarke, who along with several other council members visited Baltimore last month to see how that city has ramped up its crime camera program. Clarke says one reason Baltimore has more extensive surveillance is that the city has tapped into hundreds of private cameras at colleges, hospitals and businesses.
“Baltimore showed us how you can more comprehensively have a system that works utilizing the resources that you currently have, and taking opportunities that utilize a public/private partnership.”
Philadelphia, Clarke says, should do the same. “There are cameras throughout the city of Philadelphia, in stores, in businesses, in institutions. We simply have to figure out a way to have that partnership that allows us to utilize the feed from their cameras.”
Philadelphia has 200 surveillance cameras, while Baltimore has more than 600. And Clarke says Baltimore has retired police officers monitoring the live feeds, so criminals can often be literally caught in the act.
“When they get a 911 call, that camera automatically comes on line to a person who is actually monitoring that particular camera. That’s a very important step,” says Clarke...
(more)
(journalstar)
Lincoln police can now search for bad guys using the state's face recognition technology.
The state has used the technology for years to prevent people from getting multiple driver's licenses under different names, said Tom Casady, the city's public safety director.
Now local police trained by the state can use the same database, Casady told the Lincoln City Council last week.
Police can compare video images from a crime -- someone passing a bad check or using someone else's credit card, for example -- with the 4 million pictures in the state database of Nebraska driver's licenses, state ID photos and mug shots from jails across the state.
They also can look for the identity of someone booked into jail who refuses to give a name.
The city did try to identify a man involved in a bank robbery using the state's system, but the effort was unsuccessful because the man had a bandage on the side of his face, said Casady.
The state's technology did help to identify a disoriented man who showed up at a Lincoln emergency room, said Betty Johnson with the state Department of Motor Vehicles.
On television crime shows, the technology always works perfectly, said Casady.
It's not so easy in real life, he said.
The image has to be a good, frontal shot in order to use existing facial recognition technology, Lincoln Police Chief Jim Peschong said in a telephone interview.
In fact, drivers are asked to smile only slightly, not grin, for driver's license pictures to get the best image for facial recognition purposes, said Johnson...
(more)
Nice touch, Betty. Telling us the story about the disoriented man at the hospital being identified. And then telling us not to smile when you take our Driver's License picture. Never mind that you and your buddies will be monitoring us constantly from now on.
(msn)
It's official: The drone war has come home to America.
Wanted fugitive Christopher Dorner, the homicidal former cop currently at war with the LAPD, has become the first known human target for airborne drones on U.S. soil. Their use was confirmed by Customs and Border Patrol spokesman Ralph DeSio, who revealed the government's fear that Dorner will make a dash for the Mexican border. The fugitive has already killed three people, according to police, and has a $1 million bounty on his head. Dorner, who has military training, is believed to be hiding in the wilderness of California's San Bernardino Mountains, where locating him without air support may be all but impossible...
(more)
It's a good thing that White House memo was leaked a few days ago. You know, the one that said it was cool to drone-kill Americans?
Thursday, February 07, 2013
(abcactionnews)
The Florida Highway Patrol Troop C (Hillsborough, Pinellas, Polk, Pasco, Hernando, Sumter and Citrus counties) has announced the roads it plans to target with driver license and/or vehicle inspection checkpoints in February. FHP says the checkpoints will be conducted during daytime hours, and generally cause delays of five minutes or less.
Q: Is this legal?
A: There is a policy established by the Florida Highway Patrol that specifies the legal guidelines that must be undertaken by the agency to conduct driver license and vehicle safety inspection checkpoints. The information provided below comes directly from that policy, which was provided by FHP.
Q: How will this impact my drive? Won't these checkpoints cause big traffic jams?
A: Initially, every third vehicle will be stopped, however the Checkpoint Supervisor will monitor traffic to ensure a backup doesn't occur. If delays of more than three to five minutes occur, the Checkpoint Supervisor may order an alternate vehicle count (i.e. every fifth vehicle). If the traffic conditions cause a back up that cannot be easily alleviated by the alternate vehicle count, the Checkpoint Supervisor may temporarily suspend the checkpoint until the back-up has been cleared. Once cleared, the checkpoint can be reactivated using the last vehicle count method that was in place. Per the policy, the degree of intrusion to motorists and the length of detention to each driver should be kept to a minimum.
Q: Do these checkpoints affect trucks and buses too?
A: All vehicles and drivers, including commercial vehicles, buses and large trucks, that enter the checkpoint are subject to screening. The only exception is emergency vehicles.
Q: Isn't this profiling?
A: The FHP police states "vehicles and drivers shall not be stopped on a discretionary basis (i.e., due to the 'looks' of the vehicle or it occupant(s)."
Q: What's a "driver license checkpoint”?
A: Troopers will request the driver license and vehicle registration from each driver detained. If a driver is also the owner or registrant of the vehicle, the Trooper also may request proof of personal injury protection (PIP) insurance. FHP says violations will be enforced pursuant to Florida law and Division policy.
Q: What are" vehicle inspection checkpoints"? Troopers aren't mechanics, so why are they checking my car?
A: Per FHP, defective vehicle equipment, such as bad brakes, worn tires and defective lighting equipment, poses dangers to the public... (more)
(yahoo)
Can you spot evil in an X-ray?
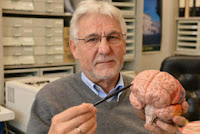
You can, at least according to a German scientist who claims an "evil patch" is visible in brain scans of criminals.
Dr. Gerhard Roth, a neurologist and professor at the University of Bremen, told London's Daily Mail that he discovered a dark mass near the front of the brain in scans of people with criminal records.
"When you look at the brain scans of hardened criminals, there are almost always severe shortcomings in the lower forehead part of the brain," Roth said. "There are cases where someone becomes criminal as a result of a tumor or an injury in that area, and after an operation to remove the tumor, that person was completely normal again."
He added, "This is definitely the region of the brain where evil is formed and where it lurks."
Roth is not alone in his belief that brain scans can reveal psychopathic tendencies.
Kent Kiehl, associate professor of psychology at the University of New Mexico, for one, used a mobile MRI unit to conduct brain scans on 2,000 prison inmates in Wisconsin and New Mexico.
Kiehl found similar patterns in their brain scans. “If you have different behavior, you’re going to have a different brain," he said at a 2012 lecture at Duke University...
(more)
(epic)
The National Highway Traffic Safety Administration has proposed regulations for event data recorders (EDR) that will become mandatory in all cars and small trucks by 2014. Building on state privacy laws, EPIC has urged the federal agency to adopt comprehensive privacy safeguards for vehicle owners and operators, including driver ownership of data, limitations on disclosure, and better security for the data collected. EPIC has also launched a national campaign to encourage public comments to the federal agency. To support EPIC’s comments Tweet: "@EPICprivacy [Your Name] supports EPIC’s EDR Comments #EDRprivacy" or email EDRprivacy@epic.org with Your Name and the subject line "I support EPIC’s EDR Comments." The public can also submit comments directly to the agency...
(more)
(wired)
The Supreme Court later this month will hear a major genetic-privacy case testing whether authorities may take DNA samples from anybody arrested for serious crimes.
The case has wide-ranging implications, because at least 27 states and the federal government have regulations requiring suspects to give a DNA sample upon some type of arrest, regardless of conviction. In all the states with such laws, DNA saliva samples are cataloged in state and federal crime-fighting databases.
The justices are reviewing a 2012 decision from Maryland’s top court, which said it was a breach of the Fourth Amendment right against unreasonable search and seizure to take, without warrants, DNA samples from suspects who have not been convicted.
The upcoming hearing, slated for Feb. 26, has drawn a huge following from civil rights groups, crime victims, federal and state prosecutors and police associations — each arguing their party lines.
The President Barack Obama administration told the justices in a filing that “DNA fingerprinting is a minimal incursion on an arrestee’s privacy interests. Those interests are already much diminished in light of an arrestee’s status and the various intrusions and restrictions to which he is subject — and that is particularly true of any interest in preventing law enforcement from obtaining his identifying information.”
On the other side, the Electronic Privacy Information Center said the indefinite retention of DNA samples raises unforeseen privacy issues.
“As our knowledge of genetics and its capabilities continues to expand, it brings with it new challenges to privacy. Once an individual’s DNA sample is in a government database, protecting that information from future exploitation becomes more difficult,” the group told the justices in a filing...
(more)
Monday, February 04, 2013
(nbclatino)
As part of immigration reform, some lawmakers want Social Security cards that come with a fingerprint. Senators John McCain (R-AZ) and Charles Schumer (D-NY) say that biometric identification could soon be required for employment. On Thursday, McCain said he was for a Social Security card with enhanced technology. Schumer supports the idea too. Likewise, President Obama has called for Social Security cards with “new methods to authenticate identity.”
Not so fast. No amount of bipartisan support can make biometric ID cards a good idea. The logistics would be a burden upon millions of Americans. The costs of creating such a system would be enormous, and the threat of a security breach constant. Not only will biometric ID cards be a tough sell to the public, they will not prevent unauthorized employment.
Consider how the introduction of a biometric Social Security card would affect the average person. Every one of our country’s 156 million workers would have to gather documents and apply at a government office in person, to be fingerprinted and issued a card. The card would be scanned at the bearer’s place of employment, and the result checked against a national database to ensure that the person is authorized to work. Even if this system were 99 percent accurate, that means 1.5 million people would be incorrectly deemed ineligible to work. Every error would result in lost wages and productivity, while the costs of obtaining correct documentation will naturally fall hardest upon the poor.
A national biometric ID would be hugely expensive. A 2012 study by the University of California at Berkeley estimated that creating such a system would cost $40 billion initially, with annual maintenance costs of $3 billion. These figures include the expenses of training workers to examine documents, issue cards, and verify employment eligibility, as well as the expenses of new hardware and software. Add into this the costs to employers, who would be required to have card scanners, which could prove problematic for medium-sized and small businesses.
Schumer wants a “non-forgeable card,” according to The Huffington Post, while McCain wants one that is “tamper-proof.” Sounds good, but is that possible? A card that is tamper-proof in 2013 may not be tamper-proof in 2023. A national database would mean that any security breach – one successful hacking into the encrypted data – would put the personal information of millions at risk of identity theft. This is a very real possibility. Between 2000 and 2008, federal and state governments mishandled or exposed 530 million records with personal data. And these are only the security breaches that have been publicly reported.
True, many Americans provide biometric data for credit cards, and our cell phones contain a trove of personal information. However, these are voluntary activities. A mandatory biometric Social Security card would be a different matter. Conservatives will decry the intrusion of government into their lives, while liberals will worry about their civil liberties. Workers would also have no way to ensure that their data is used only for its intended purpose, and not for surveillance or unauthorized monitoring. No wonder Chris Calabrese of the American Civil Liberties Union calls biometric ID cards “a massive invasion of people’s privacy...”
(more)
(nbcnews)
A confidential Justice Department memo concludes that the U.S. government can order the killing of American citizens if they are believed to be “senior operational leaders” of al-Qaida or “an associated force” -- even if there is no intelligence indicating they are engaged in an active plot to attack the U.S.
The 16-page memo, a copy of which was obtained by NBC News, provides new details about the legal reasoning behind one of the Obama administration’s most secretive and controversial polices: its dramatically increased use of drone strikes against al-Qaida suspects, including those aimed at American citizens, such as the September 2011 strike in Yemen that killed alleged al-Qaida operatives Anwar al-Awlaki and Samir Khan. Both were U.S. citizens who had never been indicted by the U.S. government nor charged with any crimes.
The secrecy surrounding such strikes is fast emerging as a central issue in this week’s hearing of White House counterterrorism adviser John Brennan, a key architect of the drone campaign, to be CIA director. Brennan was the first administration official to publicly acknowledge drone strikes in a speech last year, calling them “consistent with the inherent right of self-defense.” In a separate talk at the Northwestern University Law School in March, Attorney General Eric Holder specifically endorsed the constitutionality of targeted killings of Americans, saying they could be justified if government officials determine the target poses “an imminent threat of violent attack.”
But the confidential Justice Department “white paper” introduces a more expansive definition of self-defense or imminent attack than described by Brennan or Holder in their public speeches. It refers, for example, to what it calls a “broader concept of imminence” than actual intelligence about any ongoing plot against the U.S. homeland.
Michael Isikoff, national investigative correspondent for NBC News, talks with Rachel Maddow about a newly obtained, confidential Department of Justice white paper that hints at the details of a secret White House memo that explains the legal justifications for targeted drone strikes that kill Americans without trial in the name of national security.
“The condition that an operational leader present an ‘imminent’ threat of violent attack against the United States does not require the United States to have clear evidence that a specific attack on U.S. persons and interests will take place in the immediate future,” the memo states...
(more)
Friday, February 01, 2013
(planetbiometrics)
Social security card change could be imminent in the USA. For many years the country's social security card has been a source of criticism due to woeful security measures. Now, two leaders of the US Senate’s group looking at immigration reform, have said would endorse the idea of a biometric social security card for all Americans seeking employment.
In a joint appearance Sen. Charles E. Schumer (D-N.Y.) and Sen. John McCain (R-Ariz.) said the goal would be to stamp out illegal immigration by making it harder to forge a Social Security card and easier for employers to verify the legal status of their workers.
Schumer has reportedly said that card would be used only for employment and not as a general identification. However, he did acknowledge that there were differing opinions within the Senate’s working group and no decision had been made to include it in a bill. Clearly such a card could end up being used as an ID card - in the same way as the current document is used in many walks of life as an identity tool. So there may be an uphill battle.
Regardless, the drive to improve the security of the social security card is evident. President Obama also called for fraud and tamper-resistant Social Security documents in a White House immigration proposal released this week. The proposal also announced plans to establish a voluntary pilot program to evaluate new methods to authenticate identity and combat identity theft...
(more)